Bitcoin Optech Schnorr Taproot Workshop
In September 2019, Bitcoin Optech organized workshops in San Francisco and New York City on the schnorr/taproot softfork proposals. The aims of the workshops were to:
- share current thinking in the open source community about the proposals,
- give engineers a chance to work with the new technology through interactive jupyter notebooks, and
- help engineers take part in the community feedback process.
This blog post contains all of the videos, slides and jupyter notebooks from those workshops, so engineers at home can learn about these exciting new technologies.
The workshops were split into 4 sections:
- Preparation and basic math - shows how to set up the jupyter notebook environment, gives a refresher on basic elliptic curve math, and introduces tagged hashes.
- Schnorr signatures and MuSig - describes the bip-schnorr signature scheme and how to use MuSig to aggregate multiple public keys and partial signatures into a single pubkey/signature.
- Taproot - demonstrates how to create and then spend a segwit v1 output using either the key path (where a single signature is provided) or the script path (where a commitment to a single script or multiple scripts is embedded in a public key and later revealed and satisfied).
- Case studies - demonstrates some practical applications of the new schnorr and taproot technologies.
Slides from all the presentations can be downloaded here. Additionally, Bryan Bishop has provided a transcript of the New York session.
Introduction
John Newbery gives a summary of why schnorr and taproot are useful technologies and explains why Bitcoin Optech created the workshop. He then outlines the workshop’s aims.
Preparation and basic math
This section shows how to set up the jupyter notebook, gives a refresher on basic elliptic curve math and introduces tagged hashes.
0.1 Test Notebook
Before starting the workshops, users should follow the instructions in the repository README, clone the workshop repository and run through the test notebook to ensure that their environment is set up correctly.
→ Run this notebook in Google Colab
0.2 Elliptic Curve Math
Elichai Turkel provides a refresher on the basic elliptic curve math that will be required for this workshop.
→ Run this notebook in Google Colab
0.3 Tagged Hashes
(No video) This chapter introduces Tagged hashes, which are used in both the bip-schnorr and bip-taproot proposals.
→ Run this notebook in Google Colab
Schnorr signatures and MuSig
This section explains the bip-schnorr proposal and explains how MuSig can be used to aggregate multiple public keys and partial signatures into a single pubkey and signature.
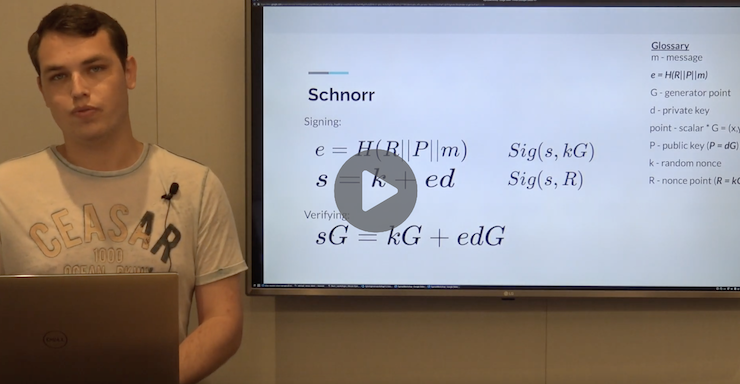
1.1 Schnorr Signatures
Elichai explains the mathematics behind schnorr signatures and explains the bip-schnorr proposal.
→ Run this notebook in Google Colab
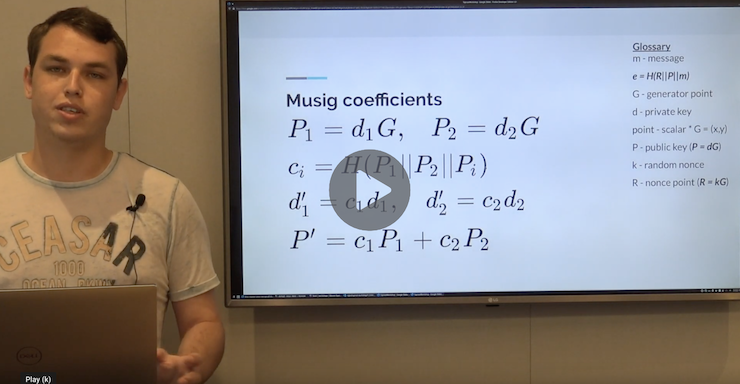
1.2 MuSig
Elichai describes the MuSig algorithm (authored by Gregory Maxwell, Andrew Poelstra, Yannick Seurin and Pieter Wuille), and shows how it can be used to aggregate multiple public keys and partial signatures into a single pubkey/signature.
→ Run this notebook in Google Colab
Taproot
This section explains the bip-taproot and bip-tapscript proposals. It shows the format of a segwit v1 output and how such an output can be spent in a key path spend or a script path spend. It demonstrates how a tweaked public key can commit to one or more scripts, and how the segwit v1 output can be spent using one of those scripts.
2.0 Introduction to Taproot
James Chiang gives an overview of the bip-taproot and bip-tapscript proposals. This notebook demonstrates how we’ll create transaction outputs, then spend them and verify that the spend is valid.
→ Run this notebook in Google Colab
2.1 Segwit V1
James shows how to create segwit v1 transaction outputs and spend them using the key path spend.
→ Run this notebook in Google Colab
2.2 Taptweak
James explains what a key tweak is, and how a tweak can be used to commit to arbitrary data.
→ Run this notebook in Google Colab
2.3 Tapscript
James discusses how we can commit a tapscript in a segwit v1 output by using a taptweak, and how we can spend that output using the segwit v1 key path spend rules. He also explains the differences between tapscript and legacy bitcoin script.
→ Run this notebook in Google Colab
2.4 Taptree
James shows how a merkle tree of scripts can be constructed, and how we can commit to that tree using a taptweak. He then explains how to spend the output by satisfying one of those scripts and providing a proof that the script was part of the committed tree.
→ Run this notebook in Google Colab
2.5 Huffman Construction
(No video) This bonus chapter shows how to most efficiently construct a tree of scripts by placing scripts that are more likely to be spent closer to the root of the tree.
→ Run this notebook in Google Colab
Case studies
This section gives demonstrations of how the new schnorr/taproot technologies can be used to build advanced Bitcoin services and products.
3.1 Degrading Multisig
(No video) This chapter demonstrates a degrading multisig wallet. In all cases, the output can be spent with a subset of the ‘live’ keys, but after some timeout, the output can be spent with a mixture of ‘live’ and ‘backup’ keys. Taproot allows multiple spending paths to be committed to, and only the one that is exercised is revealed on chain.
→ Run this notebook in Google Colab
Summary
John concludes the workshop by explaining how you can get involved in the community feedback process for these proposals.